Urgent: Windows Webcam Logs Reveal Hidden Surveillance Trail
Breaking: Windows Users Urged to Check Webcam History Immediately
Security experts are warning Windows users to inspect their webcam access logs after new analysis reveals that the operating system silently records every instance of camera activation. This hidden history, accessible through the Device Manager, can uncover unauthorized surveillance by malware or remote intruders.
“The idea that someone is switching your webcam on without you knowing is deeply unsettling,” said Dr. Elena Voss, cybersecurity researcher at CyberSafe Labs. “But most users have no idea this log exists, let alone how to interpret it.”
How to Access the Webcam History
Windows maintains a registry key (HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Foundation\HardwareMFT) that tracks enable/disable events for built-in cameras. Users can view this log by navigating to Device Manager, right-clicking the camera device, and selecting “Properties” then “Events” tab.
The log shows timestamps for when the camera was activated or deactivated. A suspicious entry during off-peak hours could indicate a breach.
Background
Webcam hacking has been a persistent threat for over a decade. Malware like Remote Access Trojans (RATs) are designed to secretly activate cameras, allowing attackers to spy on victims. Despite security improvements in Windows 10 and 11, the operating system itself records all camera activity, leaving a digital trail that can be used for detection.
In recent high-profile cases, attackers used stolen credentials to access home office webcams during remote work. The logs could have provided early evidence.
What This Means
For average users, this is a powerful tool to confirm or deny suspicions of spying. If an unknown process activated your webcam while you were away, the registry log will show it. However, advanced malware can manipulate these logs, so the absence of entries doesn’t guarantee safety.
Privacy advocates are calling on Microsoft to make this log more visible by default. “Transparency builds trust,” said Jacob Miller, digital rights lawyer. “Until then, it’s up to users to check.”

Expert Recommendations
- Check the log weekly – Look for activations when your computer was idle or sleeping.
- Use a camera cover – Even with logs, a physical slider prevents spying.
- Update security software – Anti-malware tools can detect RATs before they activate the camera.
To analyze the log, follow our step-by-step guide below.
Step-by-Step: Viewing Your Webcam History
- Right-click the Start button and select “Device Manager”.
- Expand “Cameras” or “Imaging devices”.
- Right-click your webcam and choose “Properties”.
- Go to the “Events” tab and look for “Device started” or “Started” events.
- Note the timestamps. If a start event occurs without your action, investigate.
For more on securing your webcam, see our guide on webcam privacy best practices.
Additional Privacy Measures
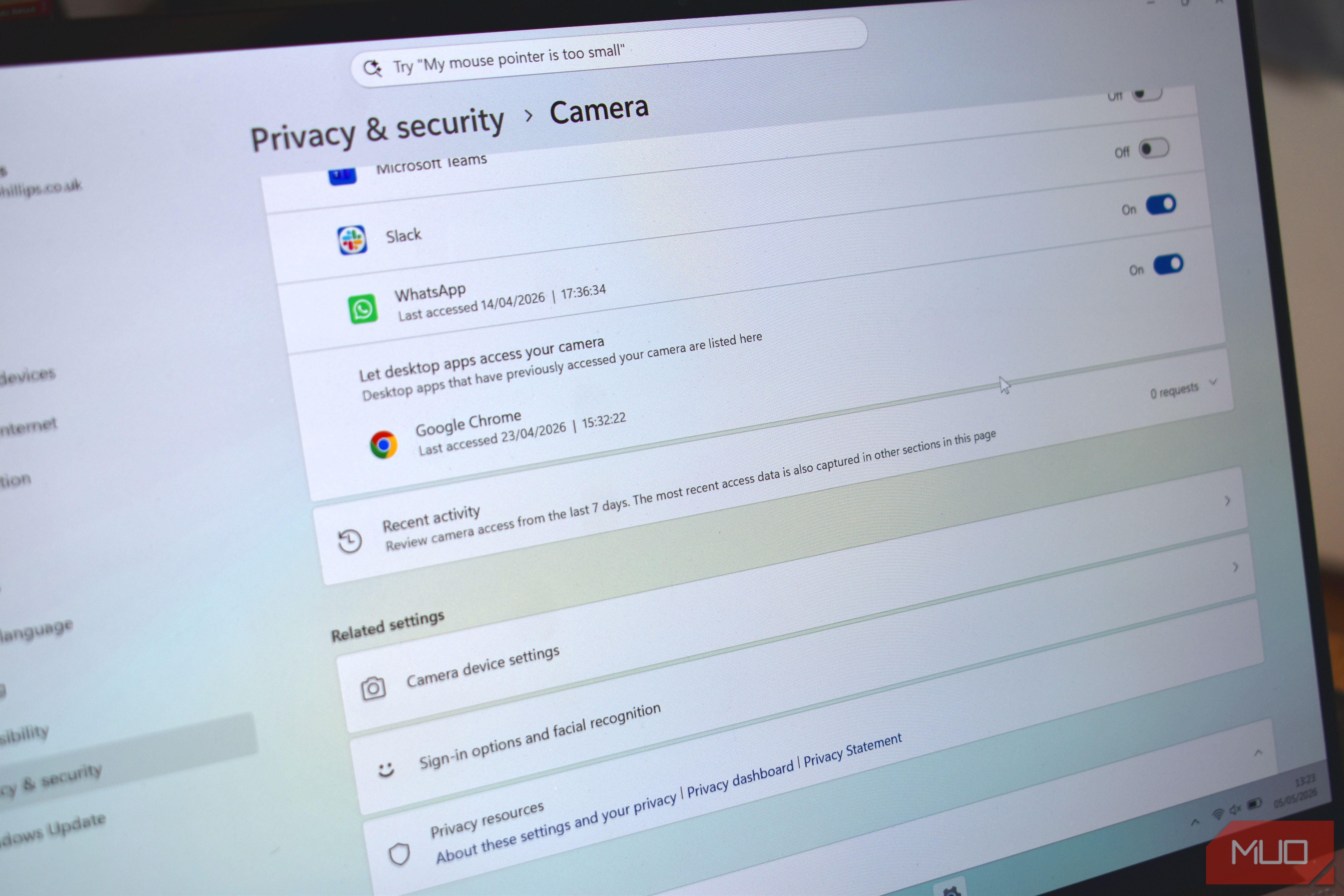
Besides checking logs, users should disable the webcam in BIOS when not needed, and restrict camera permissions in Settings under Privacy & Security. Enterprise users can enforce Group Policy to log all camera access.
“This is a simple check that could save you from a privacy nightmare,” concluded Dr. Voss. “Don’t ignore it.”
Related Articles
- Critical Supply Chain Attack Hits PyTorch Lightning and Intercom-client Packages: Credential Theft Confirmed
- DarkSword iOS Exploit Chain: A Growing Threat Across Multiple Actors and Regions
- Bleeding Llama Vulnerability Threatens 300,000 Ollama AI Deployments — Remote Exploit Without Authentication
- Cybercriminals Exploit Amazon SES to Deliver Phishing Emails That Evade Security Filters—Urgent Alert
- Massive Facebook Account Heist: Over 30,000 Compromised in New Google AppSheet Phishing Scheme
- How the Silver Fox Group Deploys the ABCDoor Backdoor via Phishing Campaigns
- Beyond the Endpoint: Unit 42 Urges Enterprises to Leverage Broader Data Sources for Threat Detection
- 8 Critical April 2026 Security Patches You Need to Install Now