Building an AI-Native Cyber Defense Strategy: A Practical Guide
Overview
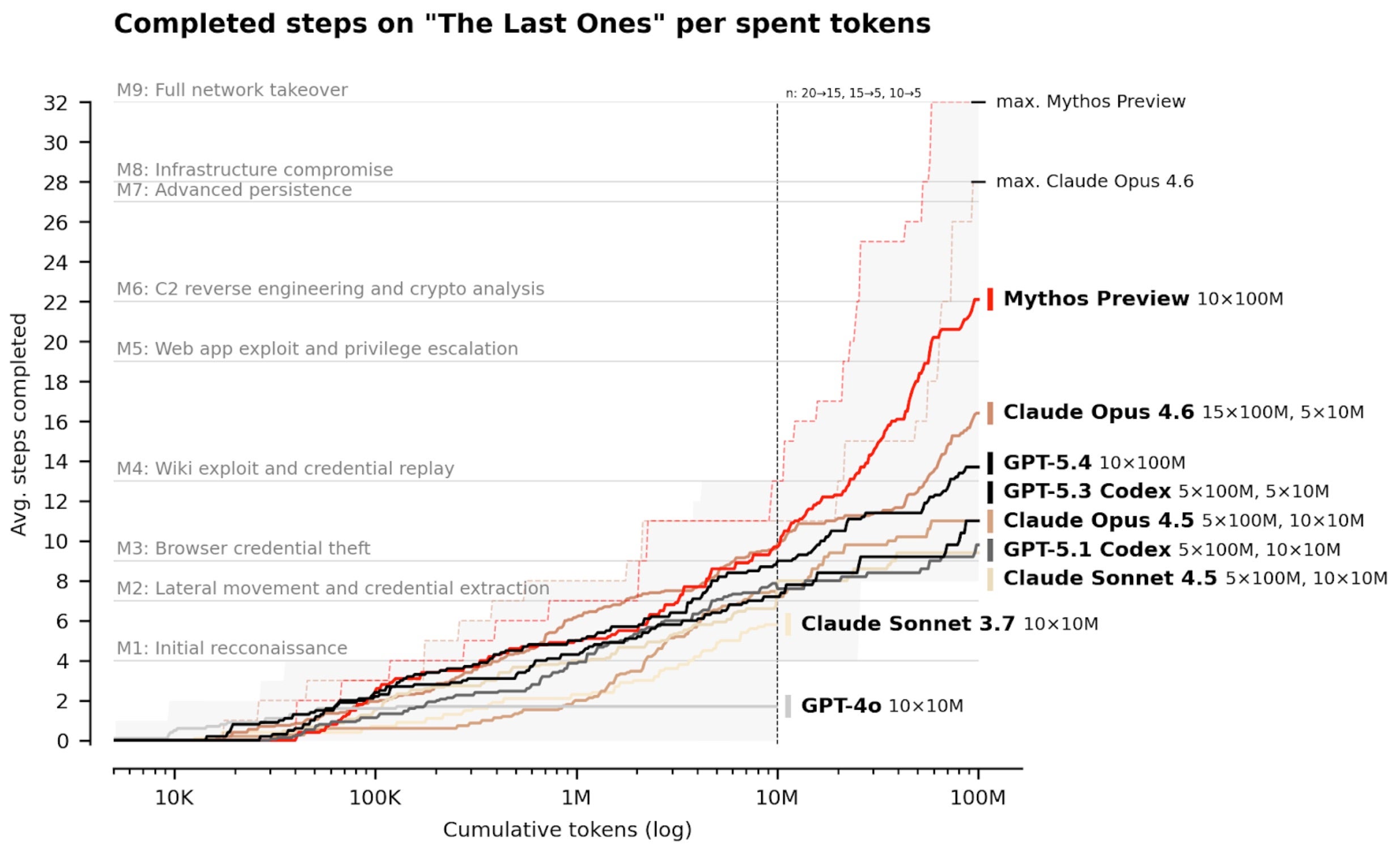
The rapid evolution of frontier AI models from labs like OpenAI, Anthropic, and Google DeepMind is transforming cybersecurity. These models are no longer just theoretical—they're being embedded into defense platforms to detect, analyze, and respond to threats at machine speed. This guide walks you through the principles and practical steps to design an AI-native cyber defense strategy, inspired by real-world implementations that stop zero-day exploits and supply chain attacks. By the end, you'll understand how to move beyond traditional vulnerability counting and toward autonomous, context-aware protection.
Prerequisites
- Basic understanding of cybersecurity concepts: familiarity with endpoints, cloud, identity, and network attack surfaces.
- Knowledge of AI/ML fundamentals: behavioral analysis, anomaly detection, and autonomous response.
- Access to a modern security platform (optional): for hands-on testing with behavioral AI features.
- Familiarity with supply chain risks: understanding of trusted agent workflows and zero-day vulnerabilities.
Step-by-Step Instructions
1. Assess the Threat Landscape: Beyond Raw Vulnerability Counts
Traditional defense focuses on patching every discovered vulnerability. However, as frontier AI enables attackers to find flaws faster, raw counts don't reflect real-world risk. Many vulnerabilities aren't exploitable in live environments due to architectural controls.
Action: Map your environment's runtime protections—sandboxing, privilege separation, and network segmentation. Prioritize threats that bypass these layers. For example, supply chain attacks (like the recent LiteLLM, Axios, and CPU-Z incidents) exploit unpatched zero-days in trusted agents. Use AI to continuously monitor behavior rather than static vulnerability lists.
2. Integrate Frontier AI Models for Contextual Analysis
Partnerships with AI labs (OpenAI, Anthropic, DeepMind) provide insights into advanced model capabilities. These models reason about attack paths, identify weaknesses in complex systems, and scale analysis across massive datasets.
Implementation:
- Deploy a security platform that ingests outputs from frontier models (e.g., GPT-4, Claude) for threat intelligence.
- Use models to correlate disparate signals—network logs, endpoint events, cloud API calls—and generate attack narratives.
- Example (pseudocode):
model.analyze(signals=['network_anomaly', 'process_injection', 'credential_access']) -> attack_path['initial_access','persistence']
3. Deploy Behavioral AI for Real-Time Detection
Behavioral AI learns normal patterns for users, devices, and applications. It detects deviations indicative of novel attacks—zero-days or unknown malware—without relying on signatures.
Step-by-step:
- Install agents on all endpoints, cloud instances, and identity providers.
- Configure behavioral baselines: CPU usage, file access patterns, network connections.
- Set thresholds for anomaly scores. For example, a process that suddenly initiates outbound connections to multiple unknown IPs triggers an alert.
- Integrate with frontier AI models to reason about anomalies: is this a false positive or a novel attack?
4. Automate Response at Machine Speed
The real advantage of AI-native defense is autonomous reaction—stopping threats in milliseconds before damage occurs. For supply chain attacks, like compromised npm packages, manual response is too slow.
Configure autonomous actions:
- Endpoint: isolate infected host, kill malicious process, rollback file changes.
- Cloud: revoke compromised IAM keys, quarantine VM.
- Network: drop suspicious connections, update firewall rules.
autonomous_policy: { trigger: 'behavioral_anomaly_score > 95', action: 'isolate_endpoint', notify: 'security_team' }
5. Span Protection Across Attack Surfaces
AI-native defense must cover endpoints, cloud, identity, data, network, and even AI pipelines (e.g., model poisoning). Use a unified platform to correlate events.
Integration tips:
- Identity: Monitor for credential theft—unusual logins, MFA fatigue attacks.
- Data: Use AI to detect data exfiltration via encrypted tunnels.
- AI pipelines: Apply behavioral models to monitor model inputs/outputs for adversarial attacks.
6. Continuously Update with Frontier Model Advancements
AI labs release improved models regularly. Maintain partnerships or subscribe to updates. Embed new capabilities (e.g., reasoning about multi-step attacks, handling multimodal data) into your detection logic.
Practical step: Create a feedback loop where security analysts label model outputs (correct/incorrect) to fine-tune detection. This is how platforms like SentinelOne evolve in real-world conditions.
Common Mistakes to Avoid
- Ignoring the gap between theoretical and operational risk: Not all vulnerabilities are exploitable. Over-patching wastes resources; focus on real-world exploitability.
- Treating frontier AI as a black box: Always validate model outputs against your environment's behavior. A model may flag benign activity as malicious.
- Delaying automation due to fear of false positives: Start with low-risk autonomous actions (e.g., notification) and gradually increase to isolation after tuning behavioral baselines.
- Neglecting supply chain trust boundaries: In the AI era, trusted agents (npm, pip, container registries) are prime targets. Ensure runtime protection for those workflows.
- Failing to update models regularly: Frontier AI evolves rapidly; static models become less effective against new attack classes.
Summary
Building an AI-native cyber defense strategy means shifting from reactive patching to proactive, autonomous protection. By integrating frontier AI models for analysis, deploying behavioral AI for detection, and automating response at machine speed, you can defend against zero-day exploits and supply chain attacks that traditional solutions miss. This guide outlined six practical steps, from assessing the threat landscape to continuous model updates. The future of cybersecurity belongs to systems that operate with AI-native intelligence—ready to outpace adversaries without human latency.
Related Articles
- Critical 'Dirty Frag' Linux Vulnerability Exposes Systems to Root Takeover; Exploit Code Now Public
- 10 Game-Changing Ways Frontier AI Is Redefining Modern Cyber Defense
- Framework’s Living Room Keyboard: A Wireless TouchPad Solution for Couch Computing
- Breaking: Zero-Day Supply Chain Attacks Neutralized—Defenses That Stop Unseen Payloads Prove Critical
- 5 Critical Insights from Google’s Latest Cyber Threat Report: AI-Driven Exploits and OpenClaw
- Ubuntu Under Siege, Linux Exploits, and Global Tech Moves: A Weekly Recap
- Yarbo's Promise: A Detailed Plan to Secure Their Robot Mowers After Critical Vulnerability
- Meta Advances End-to-End Encrypted Backups with HSM Vault Upgrades